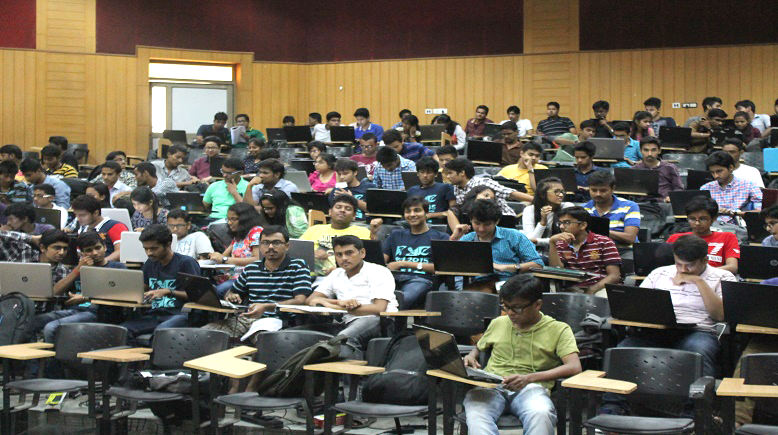
Tryst 2018 IIT Delhi
Ethical Hacking
Do You Think That Your Facebook Password's Are Safe? How Do You Know If The Transactions That You Do Are Safe Or Not? What If Someone Is Monitoring Your Gmail Accounts? What Are You Going To Do Then? Have You Ever Thought About It? Well No Need To Worry!!!
Enter Into The World Of Hacking As Ethical Hackers.
Enter At Your Own Risk…
For Assistance Call
Vivek Kumar Singh +91-8744059520Meghanad +91-8744059531 Shivani Singh +91-7065535500
Ratika +91-9990203445
Course Description
OVERVIEW
This workshop mainly focuses on the students eager to be a White Hat Hacker. It features a brief introduction to the world of hacking starting with the importance of ethical hackers and their need in today's world scenario, including to the basics of networking that will help you have a deep understanding of the working of internet.
Later, windows hacking using various methods will be introduced and in the module of steganography you will learn how to hide files in other files in order to protect sensitive data. After the end of the aforementioned module you will be learning phishing in which you will be taught How to hack Facebook Accounts and Gmail Accounts and thus how to avoid it.
In the end you will gain knowledge about the basics of Backtrack 5 and the concept of man in the middle attack (MITM ATTACK).
The duration of this workshop will be 1 day , with 3 Sessions , 3 hours each, properly divided into theory and hand on practical sessions.
Certificate by RoboTryst 2018 in Association With Tryst 2018 IIT Delhi
Best Suited For: All B.Tech/B.E./BCA/BSc Students
Day 1 (Session 1)
Ethics and Hacking
- Hacking History- How It All Began
- Need For Ethical Hacking
- Why We Require Ethical Hackers
- Types Of Hackers
- Steps In Ethical Hacking
- Scopes In Hacking
Windows Hacking
- To exploit the vulnerabilities of windows using live devices and Universal Serial Bus (USB).
Steganography
- What is Steganography?
- Hiding data behind Images, PDFs, Audio and Videos files
Day 1 (Session 2)
Basics Of Internet, Networking And Hacking
- What is a Network?
- Types of network – LANs, WANs & WLANs
- What is Internet?
- Basic Structure
- What is a Server?
- What is an IP Address?
- What is a domain name?
- IP-Domain Relation
- Client-Server Relationship Model
- Internet networking
- Set up Ad-hoc networks
- Basic explanation of exploitation of loopholes
SQL Injection Using DVWA
- Introduction of SQL
- What are SQL INJECTION and DVWA?
- Checking SQL injection vulnerability (Demo)
- Live demonstration of the attack (Demo)
- How to protect your system from attacks
Day 1 (Session 3)
Man In The Middle Attack(MITM)
- What is Backtrack Linux?
- What is Kali Linux?
- What is Man-in-the-middle attack?
- Preparation for Man-in-the-middle attack (Demo)
- Setting Ettercap tool for the attack (Demo)
Phishing
- What is phishing?
- Preparation for phishing
- Phishing using Local server
Trojan, Worms And Viruses
- Introduction to the concepts of Trojans, worms and viruses
- How to use Virtual Machine (Live Demo)
- How to use Backtrack (Live Demo)
- Fake Mail
Project to be Covered
- Phishing (Internet And Domain Required)
- Steganography
- MITM (Internet Required)
- SQL Injection Using Dvwa
- Windows Hacking
- Fake Email (Internet Required)
- Creation Of Trojans And Viruses